how Keyloggers get around OS X security
With the release of Elite Keylogger Version 1.7.327, we’ve noticed some unexpected changes to how the developers are installing and hiding their work.
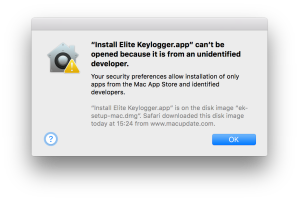
Let’s take a quick look at what happens when you install the free demo of this keylogger. First, you’ll notice that the app isn’t codesigned and requires you to override any GateKeeper settings.
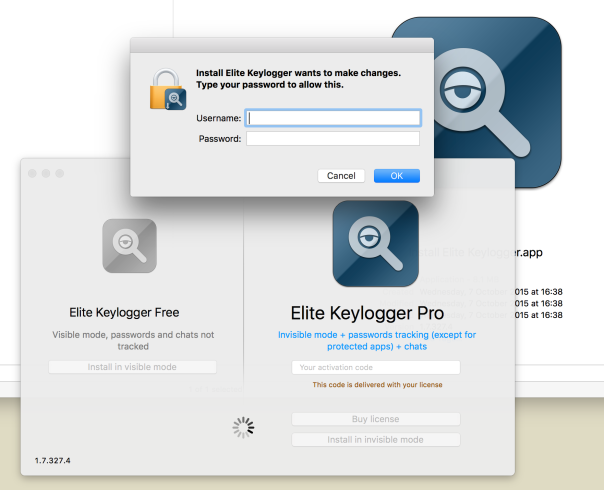
Secondly, it’ll ask you for your admin password to escalate its privileges so it can write to wherever it wants in the system. So far nothing new. But here’s where the new release gets interesting.
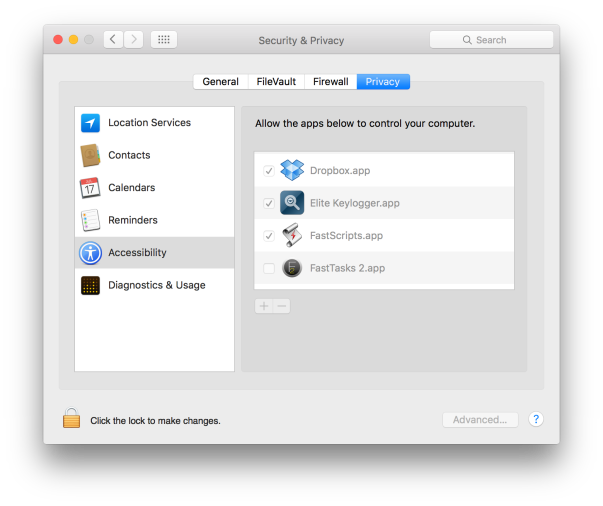
What it does next is automagically insert itself into System Preferences/Security & Privacy/Privacy/Accessibility without throwing the required authorisation dialogue:
Forcing apps to be in this list if they want to leverage System Events to control a computer was a change brought in with OS X Lion 10.7, and it isn’t supposed to be circumventable.
The idea was that to get in this list, apps were forced to throw an authorisation dialog to get the user’s permission, even if the user had already given the app admin privileges elsewhere.
Unofficially, we’ve heard that Apple had once promised to crackdown on developers who tried to circumvent this security feature and to close any gaps that were exposed. As it is, we’ve not only been aware of a way around this security feature since late 2013, but it seems it’s not just the less reputable that are at it. Dropbox has been inserting itself into the Accessibility list since at least 10.10.5, without asking for permissions (in our screenshot, we never authorised either of these apps to be in this list, nor did we ever unlock the padlock to let them in).
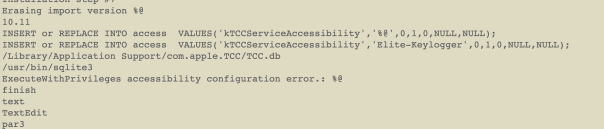
The way that Elite Keylogger does this is through a sql database insertion, you can see the code they use here:
Another interesting development is that Elite’s developers, widestep, are now leveraging a hidden binary called FScript64 that is placed and hidden with the chflags -hidden flag set here:
/Library/ScriptingAdditions/FScript64.osax
We first saw this binary used in Refog’s Hoverwatch keylogger, but this is the first time we’ve seen the same code shared with other keyloggers. We can only speculate as to why developers from apparently-competing products are sharing code.
A couple of other things to note with Elite: If you drag the app to the Trash, the secret FScript64.osax will be left behind. If you use the uninstaller, the hidden binary will be removed, but another hidden data file will be placed here:
~/.ek
Our troubleshooting app DetectX already knows about both of these files, so if you want to check whether you’ve got rid of both of these or have other keylogger files present, download a free copy from sqwarq.com.
DetectX registers the addition of Elite Keylogger
Finally, note that even if you use Elite Keylogger’s uninstaller, the app will remain in the list of Accessibility apps and it will remain in your list of login items. You’ll need to manually remove them both, and the hidden .ek file AND the osax if you didn’t use the uninstaller or didn’t use DetectX to help you remove the crud.
As always, be careful about what you download, use apps like DetectX or FastTasks 2 that can log changes that downloaded apps make to your system, and beware of all apps that require your admin password in order to be installed. There are legitimate reasons for that in some cases, but not many.
Posted on November 16, 2015, in Security-2 and tagged keyloggers. Bookmark the permalink. Leave a comment.

Leave a comment
Comments 0