Category Archives: Safari
adware extensions erode trust in Apple, Google app stores
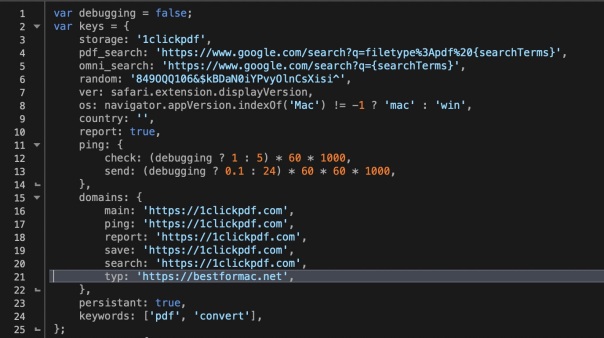
Browser extensions are a staple of almost every user’s set up. Even in managed environments, users are often able to install extensions or ‘Add Ons’ without authorisation when these are sourced from trusted sources like Apple’s Safari Extensions Gallery and Google’s Chrome store. Of course, there’s nothing new about attackers exploiting the browser extension as a means to gaining a foothold in a target environment. The problem has been around for years: what is surprising is just how difficult it is to contain the problem. In this post, I take a look at the risks involved with what appears to be a harmless extension available for both Safari and Chrome. As we’ll find out, not everything appears as it seems.
DuckDuckGo Privacy Extension not so private

DuckDuckGo recently made changes to their browser extension which turns it into an adblocker and privacy advocate, stalling websites that would like to track you and sell your behaviour to the nearest (not necessarily highest) bidder.
It sounds great, until you install the extension and realise you’re trading one privacy exposure for another. As the picture above makes clear, you’re allowing the extension to read everything you post on a website, including your passwords. To be fair, this is not uncommon with adblockers, but it is also not necessary; 1Blocker and Better adblocker, for a couple of examples, do it properly:
I don’t know who’s really behind DuckDuckGo or what they really do with the data they can see from my web browsing. I know no more about them than I know about those behind all the adtrackers and other spyware that the DuckDuckGo extension is trying to block (while being able to read my passwords and potentially track my browsing habits).
DuckDuckGo may have a good reputation, but there’s a whiff of the hypocritical in a tool that promises to protect you from spying that can itself potentially spy on you.
Sorry, but that’s not the kind of tool I need to protect my privacy. I immediately uninstalled it.
malware can make Safari windows invisible
Given news that some hackers are using websites to mine cryptocurrency even when users apparently close their browser on Windows, I got to wondering whether a similar exploit would work on macOS.
As the video above shows*, a malicious app can easily hide an open Safari window from all desktop workspaces, making it incredibly difficult for users to notice or to make visible again even when they do. This trick can be exploited without elevated privileges, and it doesn’t matter whether the malicious app is code-signed or not.
An invisible Safari window is a problem because it could be running scripts, mining cryptocurrency, redirecting to sites for adware revenue or doing all manner of other things. Note the window could contain multiple tabs that the user may have already been tricked into opening before the window is made invisible.
As can be seen in the video, the Safari window isn’t in another full screen workspace, or minimized in the Dock or hidden by any other window or toolbar (as in the Windows 10 trick).
On the contrary, it can’t actually be found anywhere, and nor will Window > Bring All To Front help. If you open a new window and then try to use Merge All Windows to bring the hidden window out, all that happens is your new window will disappear with the hidden window too.
The only visible indicators that there’s an invisible window open are the window list in the Window menu, and the invisible outline revealed by Expose (four-finger swipe down).
So what if you find there is an invisible window hiding from you, how do you get it back?
To retrieve and kill the hidden window, you need to click View > Enter Full Screen, then click the red close button. Don’t click the green button to take it out of full screen though, as that’ll just cause it to hide again, with a nice animation that you can see on the video!
Another day, another hacker trick to watch out for folks!
* This vulnerability was demonstrated on 10.12.6. It also exists in both 10.11.6 El Capitan and 10.13.2 High Sierra.
news: App Fixer 1.2 released
We’ve just released App Fixer 1.2, available for free download from here.
If you’re not familiar with this junior partner in our troubleshooting suite of apps, App Fixer does a very specific job: it returns any app you select to its default preferences and settings with the click of a button.
It’s raison d’être is largely for those apps that get themselves stuck in some unresponsive state (looking at you anything-Adobe). It also does a neat trick rescuing Safari from Adware on the side. ;).
If you’ve been using App Fixer already and you’re currently running El Capitan, we’re afraid you won’t see an update notice (the blame for that lies with Amazon AWS, but that’s another story). Just go to the App Fixer home page and download directly. We’ll be introducing an in-app updater (Sparkle) in the next release to make future updates more convenient.
how to block Flash in Safari
If you’re worried about news like yet another Flash vulnerability, the first thing to note is that Apple has moved to block all but the latest version.
However, given that exploits of Flash seem to occur sometimes within days of even new releases, it might be wise to think about blocking Flash altogether in your day-to-day browser.
Fortunately, that’s pretty easy to do in Safari. Just go to Safari’s Preferences > Security tab, and uncheck the ‘Allow Plug-ins’ box at the bottom. You can manage which websites are allowed access to Flash from the adjacent button, but an alternative strategy is to use a different browser (Firefox or Opera for example) for only viewing sites where you need Flash access.
Either way, its seems wise to make sure that Flash isn’t allowed unrestricted access on your main browser.


