Blog Archives
latest MacKeeper file paths
Most recent update: Mon 3 Sep 2018
Want to remove MacKeeper? The easiest way is to use my free/shareware app DetectX Swift, but if you’re looking to do it yourself, here’s the complete list of all past and current known filepaths.
Bear in mind that DetectX Swift can find other MacKeeper paths that are not on the list due to its internal search heuristics; however, I’ll update this list as new paths come to light. If you happen to find any that are not on the list, please share in the comments!
Thx & Enjoy!
Paths
$TMPDIR/MacKeeperUninstaller.app
$TMPDIR/com.mackeeper.MacKeeper.Installer.config
/Applications/MacKeeper.app
/Applications/Utilities/MacKeeper.app
/Library/Application Support/MacKeeper
/Library/Application Support/MacKeeper/AntiVirus.app
/Library/Application Support/MacKeeper/AntiVirus.app/Contents/MacOS/AntiVirus
/Library/Application Support/MacKeeper/MacKeeperATd
/Library/Application Support/MacKeeper/MacKeeperTrackMyMacDaemon
/Library/LaunchDaemons/com.mackeeper.AdwareAnalyzer.AdwareAnalyzerPrivilegedHelper.plist
/Library/LaunchDaemons/com.mackeeper.AntiVirus.plist
/Library/LaunchDaemons/com.mackeeper.MacKeeperTrackMyMacDaemon.plist
/Library/LaunchDaemons/com.mackeeper.MacKeeperPrivilegedHelper.plist
/Library/LaunchDaemons/com.mackeeper.MacKeeper.MacKeeperPrivilegedHelper.plist
/Library/LaunchDaemons/com.mackeeper.MacKeeper.plugin.AntiTheft.daemon
/Library/LaunchDaemons/com.mackeeper.plugin.AntiTheft.daemon
/Library/LaunchDaemons/com.zeobit.MacKeeper.AntiVirus
/Library/LaunchDaemons/com.zeobit.MacKeeper.AntiVirus.plist
/Library/LaunchDaemons/com.zeobit.MacKeeper.plugin.AntiTheft.daemon
/Library/PrivilegedHelperTools/com.mackeeper.AdwareAnalyzer.AdwareAnalyzerPrivilegedHelper
/Library/PrivilegedHelperTools/com.mackeeper.Cerberus
/Library/PrivilegedHelperTools/com.mackeeper.MacKeeperPrivilegedHelper
/Library/LaunchDaemons/com.zeobit.MacKeeper.plugin.AntiTheft.daemon.plist
/Library/Security/SecurityAgentPlugins/MKAuthPlugin.bundle -- warning: deleting this file could harm your Mac! Contact me for help.
~/Applications/mackeeper.app
~/Applications/Utilities/mackeeper.app
~/Documents/MacKeeper Backups
~/Downloads/MacKeeper.3.12.1.pkg
~/Downloads/MacKeeper.3.16.4.pkg
~/Downloads/MacKeeper.pkg
~/Library/Application Support/com.kromtech.AdwareBuster
~/Library/Application Support/com.kromtech.AdwareBusterAgent
~/Library/Application Support/com.mackeeper.AdwareAnalyzer
~/Library/Application Support/com.mackeeper.MacKeeper
~/Library/Application Support/com.mackeeper.MacKeeper.Helper
~/Library/Application Support/com.mackeeper.MacKeeper.MKCleanService
~/Library/Application Support/com.mackeeper.MacKeeper.Uninstaller
~/Library/Application Support/com.mackeeper.MacKeeperAgent
~/Library/Application Support/MacKeeper
~/Library/Application Support/MacKeeper 3
~/Library/Application Support/MacKeeper Helper
~/Library/Caches/com.mackeeper.MacKeeper
~/Library/Caches/com.mackeeper.MacKeeper.Helper
~/Library/Caches/com.mackeeper.MacKeeper.MKCleanService
~/Library/Caches/com.zeobit.mackeeper
~/Library/Caches/com.zeobit.mackeeper.helper
~/Library/LaunchAgents/com.kromtech.AdwareBusterAgent.plist
~/Library/LaunchAgents/com.mackeeper.AdwareAnalyzer.plist
~/Library/LaunchAgents/com.mackeeper.MacKeeper.Helper.plist
~/Library/LaunchAgents/com.mackeeper.MacKeeperAgent.plist
~/Library/LaunchAgents/com.zeobit.mackeeper.helper
~/Library/LaunchAgents/com.zeobit.mackeeper.plugin.backup.agent
~/Library/Logs/MacKeeper
~/Library/Logs/MacKeeper/MacKeeper.log.db
~/Library/Logs/MacKeeper.Duplicates.log
~/Library/Logs/MacKeeper.log
~/Library/Logs/MacKeeper.log.signed
~/Library/Preferences/com.mackeeper.MacKeeperAgent.plist
~/Library/Preferences/com.mackeeper.MacKeeper.Helper.plist
~/Library/Preferences/com.mackeeper.MacKeeper.plist
~/Library/Preferences/com.zeobit.mackeeper.helper.plist
~/Library/Preferences/com.zeobit.mackeeper.plist
~/MacKeeper Backups
Bundle Identifiers & Launch Labels
com.kromtech.AdwareBuster
com.kromtech.AdwareBuster.AdwareBusterPrivilegedHelper
com.mackeeper.AdwareAnalyzer
com.mackeeper.AdwareAnalyzer.AdwareAnalyzerPrivilegedHelper
com.mackeeper.AntiVirus
com.mackeeper.Cerberus
com.mackeeper.Kira
com.mackeeper.macKeeper
com.mackeeper.MacKeeper.MacKeeperPrivilegedHelper
com.mackeeper.MacKeeper.plugin.AntiTheft
com.mackeeper.MacKeeper.plugin.MKAuthPlugin
com.mackeeper.MacKeeperTrackMyMacDaemon
com.mackeeper.MacKeeper.Uninstaller
com.mackeeper.MacKeeperAgent
com.mackeeper.MKFoundation
com.mackeeper.MKUIKit
com.mackeeper.plugin.AntiTheft
com.mackeeper.WPAdwareUtils
com.zeobit.MacKeeper.AntiVirus
com.zeobit.MacKeeper.plugin.AntiTheft
Related:
how to uninstall MacKeeper
Mac Media Player’s secret MacKeeper installer
Last week I added MacGo’s Mac Media Player.app to DetectX’s search definitions after finding that the installer was delivering MacKeeper on unsuspecting users. After a support call asking me whether the MacGo player itself was malicious, I decided to look into what was going on in a bit more detail.
Downloading the Mac Media Player from the developer’s site rewarded me with a DMG file called Macgo_Mac_Media_Player.dmg, and mounting that revealed the Installer.app (pictured above).
Examining the package contents of Installer.app had a few surprises. For one thing, the bundle identifier (a reverse domain-name style string used to uniquely identify an app on macOS) was the oddly titled com.throbber.tipcat, and the executable binary file was named hemorrhoid. Examining both the binary and other files in the Installer bundle revealed some heavily obfuscated code that is really quite unusual to see in anything except malware.
That gave me pause to try and run the Installer in the lldb debugger and see exactly what it was up to, but – also another sign of malware – the Installer.app appears to have been coded precisely to stop that from being possible. Every time I tried to attach the debugger to the Installer’s process, the installer quit with “status = 45”, a sign that the debugger is being deliberately thwarted.
My next tack was to dump the class names with
otool -oV /Volumes/Installer/Installer.app/Contents/MacOS/hemorrhoid | grep name | awk '{print $3}'
And that revealed some oddities, too. With names like ‘stockyardsStormed’ and ‘DefilersDiesels’ I was sufficiently intrigued to run the installer to completion and see it in action. As the screenshots below from my shareware troubleshooter DetectX and Objective Development’s Little Snitch 4 indicate, the unwary will get a lot more than just a free video player:
Finally, just to confirm my results, I uploaded the installer.app to VirusTotal, and found that it was a variant of the InstallCore strain of adware.
That pretty much wraps up the case against the installer, but what about the Mac Media Player app and its related version the Macgo Mac Blu-ray Player Pro? It seemed as far as I could tell that the apps themselves were ‘clean’. However, RB AppChecker Lite reveals that the installer and both the apps are signed with the same Apple Developer ID, ZJ Tech Inc, F9QTW5KSLJ.
That pretty much rules out any possibility that the developers had been unknowingly compromised. Clearly, ZJ Tech are quite happy to distribute their software to customers and do a stealth install of MacKeeper at the same time. Presumably, there’s some financial pay-off for them in doing that. Given that ZJ’s media players also seem to be little more than copies of VLC.app, it seems there’s pretty good reason enough to avoid using their products.
scan for malware on the command line
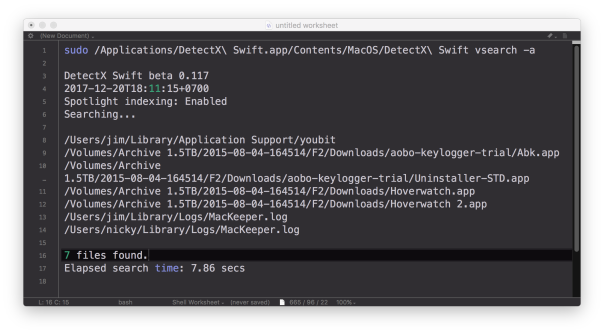
DetectX Swift now has the ability to do command line searches for issues on your mac like malware, keyloggers, browser hijacks and potentially dangerous software, and there’s a number of extra options that are not available when using the user interface. In this post, I’m going to give you a quick tour of the CLI (Command Line Interface) tool with some examples of how to use it (if you haven’t yet grabbed a free copy of DetectX Swift you might want to do that first to play along).
1. Basic scan
Let’s start with a basic scan. To use the CLI search, you need to specify the full path to the app executable. In this example, let’s suppose that the app is in /Applications folder. In that case, you’d need to execute this on the command line:
/Applications/DetectX\ Swift.app/Contents/MacOS/DetectX\ Swift search
Since that’s a bit of a handful, even using tab completion, you might want to edit your .bash_profile to include a shortcut alias. Here’s mine:
sphil@sphils-iMac-5:~$ cat .bash_profile
alias sudo='sudo '
alias detectx='/Applications/DetectX\ Swift.app/Contents/MacOS/DetectX\ Swift'
Note the sudo line (and note the extra space in the value). We’re going to need that so that we can pass the alias to sudo when we want to pass certain options to the search. Like…
2. Scan other users
Probably the most important benefit you gain with scanning on the command line rather than from the app’s interface is the ability to scan all, or selected, other users. You can search all users by using sudo and the -a option:
sudo detectx search -a
If you want to restrict the search to one or more users, the -u option allows you to specify a list of shortuser names (comma-delimited):
sudo detectx search -u alice,bob
3. Go deep
If you’d like more verbose output, including how long the search took, try either the vsearch or vvvv commands:
sudo detectx vvvv -a
4. Save the results
You can specify a path to output the results, either in regular text:
sudo detectx vvvv -a ~/Desktop/searchtest.txt
or, by passing the extra -j option, in JSON format:
sudo detectx search -aj ~/Desktop/searchtest.json
Here’s an example of what the formatted JSON file looks like:

5. Anything else?
There’s a help command that will output the documentation to the command line, and also if you get into the habit of regularly running command line checks, don’t forget to launch the app from time to time in the Finder. Like its predecessor, DetectX, DetectX Swift does a lot of other stuff besides searching that can help track down and remediate problems with your mac, and a large part of that revolves around the way it tracks changes to your system every time you launch it. The CLI tool runs independently of that and won’t give you that kind of feedback or record those changes.
Finally, note that in the release version of DetectX Swift, the CLI tool is only available for a limited period to Home and Unregistered users. Unlimited acccess to the CLI tool requires a Pro or Management license.
Enjoy! 🙂
how to keep the iDoctor away

DetectX has been updated today to v2.37, and amongst other changes now detects and removes iDoctor.app. This piece of software appears to be another MacKeeper clone, with both sharing a common interface, code and file structures.
In the screenshot above, you can see DetectX doing its work – note the parallel file detections as DetectX hunts down both MacKeeper and iDoctor.
Below is a sidebar shot of MacKeeper on the left and iDoctor on the right. Underneath that are shots showing how the two interfaces are almost direct mirrors of each other. It’s hard to believe these are not both being built from the same base code, and we strongly suspect that the developers of iDoctor are very likely the same developers of MacKeeper, or at least real close friends!



news: DetectX v2.14 released
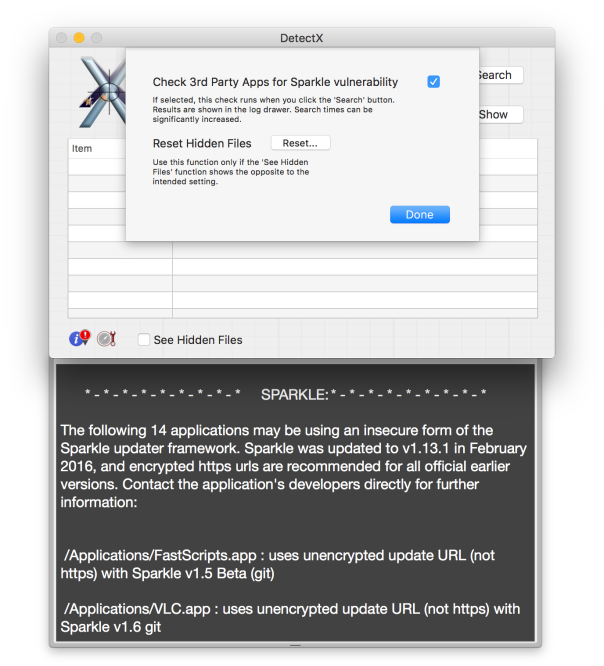
Yes, two in two days! We’ve added a Preference Pane since yesterday, and improved the performance of the search function. Note that the new Sparkle Vulnerability check we introduced in v2.13 is now off by default. It can be turned on from the Preference Pane (see above).
Other changes are listed in the release notes.
DetectX is still free, fully-functional, and without time-limit for home users. Available for download from here.
🙂
news: FastTasks v2.4 update released
FT2 v2.4 is now available from sqwarq.com.
This update includes a new ‘delete’ button in the Analyser and an auto-kill feature which searches for and kills MacKeeper processes running in the background when the Analyser is run.
The release notes are here.
how to uninstall MacBooster

We are decidedly not impressed with MacBooster. Ok, we’ll put aside the general complaint that apps like this do very little if anything to improve performance (in fact, in our tests, we find almost always quite the opposite). We have a bigger beef with MacBooster.
Indeed, we rate it even more pesky than it’s obvious inspiration: MacKeeper…😳
Aside from the fact that MacBooster’s uninstaller leaves a number of executables and other binary files hidden on the user’s system, there’s also the rather cheeky use of ‘com.apple.UninstallerAD” as a bundle identifier in their uninstaller app.
I really don’t think the folks at Cupertino are going to appreciate that, but more importantly the use of a misleading bundle identifier reveals a lot about the developers’ intentions.
We’ve added MacBooster to DetectX (v.2.06) and it will be included in the next update to FastTasks 2.
Meanwhile, whether you use our apps or not, steer clear of MacBooster.
If you’d rather dig it out yourself than use DetectX, here’s the list of paths we have so far:
/Applications/MacBooster 3.app/Users/Shared/MacBooster/FileData3/Users/Shared/MacBooster/Boost3.plist/Users/Shared/MacBooster/Library/Caches/AMCExtractByte/Library/Caches/AMCInstallTemp.txt/Library/Application Support/AMC/Library/LaunchDaemons/com.iobit.AMCDaemon.plist~/Library/LaunchAgents/com.iobit.MacBoosterMini.plist~/Library/Application Support/ErrorReporter~/Library/Application Support/MacBooster~/Library/Application Support/MacBooster 3.0~/Library/Preferences/cryptFile3~/Library/Preferences/com.iobit.Boost3.plist~/Library/Preferences/com.iobit.MacBooster-3.plist~/Library/Preferences/com.iobit.MacBooster-mini.plist
news: DetectX 2 is available now
We’ve spent pretty much the whole of the summer working on this upgrade, so we’re both delighted (and not a little relieved!) to finally be able to announce the release of DetectX 2.
If you were a user of earlier versions of DetectX the most obvious change you’ll notice is the new Selector bar, and the additional functions it offers. Now, DetectX is far more than just a dedicated search tool and offers comprehensive logging, browsing and analytical tools to make troubleshooting new problems on your mac a whole lot easier.
If you’ve used the Analyser in our app FastTasks 2, you’ll recognize the new functions added to DetectX. But we’ve not just taken the Analyser straight out of FT2 and plumped it into DetectX, we’ve also made it more powerful and more convenient to use.
There’s a whole bunch of changes you can find out about from the DetectX page and from the included user guide (improved documentation is another one of the changes!). One thing that hasn’t changed: DetectX remains free for home users, so there’s nothing to stop you from trying it out. Commercial and institutional users should note that a Commercial Use licence is required. Details are in the app.
Well, now that the app is out you’d think we’d be taking a break, but we’re already working on a special release of DetectX for Snow Leopard users. We know you 10.6’ers have been left out in the cold since release 1.29, but hold tight. Some Leopardy love is coming your way real soon!
On top of that, we’re already working on new definitions to be added to the next update to make sure DetectX keeps finding all those new annoyances that keep popping up and keeping your Mac happy and responsive.
If you haven’t already, go check out the DetectX page for more info.
protect your mac from malware, viruses and other threats

If you’re new to Mac, you’re probably thinking that it’s a no-brainer that you need some kind of anti-virus app. Once you start looking around the web for reviews, it’s inevitable that you’re going to come across the Great Mac AntiVirus Debate: in the one corner, those who say Mac users who forego antivirus protection are arrogant and just setting themselves up for a fall, and in the other those who’ve used Macs for umpteen years, never had or heard of any real threat, and consequently say AV software is a waste of time.
You can read round this debate for years and never come to a satisfying conclusion, largely because its as much about what you ‘ought’ to do as it is about what is the case. Just because you’ve never had any viruses, doesn’t mean you won’t get one tomorrow. And yet, there are NO viruses in the wild known to affect macs, and so when one does arrive, it will be unknown to your AV scanner. Hence, an AV Scanner is just a waste of system resources (and possibly money, if you paid for it). Yikes! What do I do!!
What you do is sidestep the whole debate and stop thinking only about virus scanners, which after all deal with only a small subset of all the possible attack vectors in the internet age, and start thinking in terms of vulnerability scanners. Unlike a simple virus scanner, a vulnerability scanner examines your system not only for malware but also for any vulnerabilities in commercial software, plug ins, your system setup (including network and other sharing settings) and other installed items. The scanner will not only explain the threat and its severity but also tell you what, if anything, you need to do, recommend patches and guide you to links for more info where available.
You can use something like Nessus for free if you are a home user, which will give you a far better insight into the possible attacks someone could implement on your system (and it will check your system against almost all of the major virus scanner databases like Symantec, etc).
Even better, a vulnerability scanner like Nessus won’t just examine your machine, it’ll look at everything else (and all the installed apps) of anything on your home network including phones (any platform), other computer systems (any OS), and even your router.
block MacKeeper and other browser ads
Generally, I like to keep browser extensions down to a minimum, but here’s an essential one if you are tired of all those ‘Clean your mac’ / ‘Speed up your mac’ ads on every website you visit. Download and install the Safari adblock extension from here:
What I like about this particular adblocker is that, if you go with the default filters, not only does it load your pages faster but it also reformats the page as if the ads were never even there, rather than leaving unsightly, blank placeholders in the page as some other ad filtering services do.
The extension is free, though you’re encouraged to donate if you appreciate the work done by the developer.
🙂
Related Posts
how to uninstall MacKeeper








